Access control authentication technologies have been evolving for decades but the COVID-19 pandemic has accelerated the process, pushing users towards use of mobile authentication technologies and face recognition faster than ever before.
ACCESS control authentication technologies are a curious hybrid of the analogue and the digital, with keypads and carried credentials competing with biometric readers, biometric-powered smart devices and video analytics-driven face recognition technologies in an increasingly sophisticated access control market.
The question for integrators and end users is which technology will prevail, given there are significant capital and operational expenses associated with each choice. Operational issues that must be considered include providing a low touch environment, minimising or eliminating the expense of card library management, overcoming user worries about biometric technologies, and ensuring access control providers have relevant technology partnerships with developers.
Over-arching these considerations will be questions of credential security, risks revolving around network exposure and the challenges of managing multi-authentication enterprise applications, in which cards and smart devices may rub shoulders with face recognition and fingerprint scanners. Given support from the underlying access control solution, such systems may offer stronger authentication in some locations and more affordable authentication in others.
According to Gallagher’s Steve Bell, the most secure of all access authentication technologies is a public key-based authenticator.
“This is considered the most secure authentication technology as it is less vulnerable to attacks, compared to symmetric key authenticators and biometric authenticators,” Bell explains.
“MIFARE DESFire cards are an example of a symmetric key authenticator. An access control system incorporating MIFARE DESFire cards requires a shared secret key that must be available at each reader to be able to authenticate with the card applet, prior to reading the credential information from the card.
“Examples of a public key authenticator include a smart card with a certificate (e.g., USA Government FIPS201-2 standard), or a simpler FIDO authenticator that is now built into all new IOS, Android, and Windows devices. The advantages of public key technology are that any security vulnerability that leaks a public key does not allow an attacker to impersonate that authenticator.”
According to Bell, the USA National Institute of Standards (NIST) standard SP800-63B documents its view of the strengths and weaknesses of various authentication technology alternatives.
“Symmetric authenticator systems rely on the shared secret key being kept secure at each reader,” Bell explains. “Should a reader become compromised, the keys need to be rolled or migrated across each card. Public key authenticators depend on the ‘relying party’. The device wanting to authenticate the credential must know the public key for the matching private key on the authenticator, and this is more technically complex for the device vendors to achieve, but is significantly more secure.”
Bell argues that any access control authentication solution should also include the option for second factor authentication for greater certainty, such as a PIN number or biometric.
“Interestingly, NIST does not consider a biometric authenticator alone to be sufficiently secure,” Bell says. “This is due to a biometric authenticator acting on probability that it is reading the correct person, in comparison to a cryptographic authenticator which can determine a person’s authentication.”
Cost is a key element of choice when it comes to authentication technologies but these days it’s harder to establish which technology has the lowest total cost of ownership over the lifetime of a system. There are ongoing costs associated with using physical credentials.
“Card-based authenticators such as MIFARE DESFire EV2 (or EV3) are the best of breed for the current generation of access cards,” argues Bell. “However, the total cost of ownership includes, enrolling a person into the system, including their name and select personal information, as well as photo capture, the physical card cost, encoding the credential onto the card, printing the photo and other information onto the card, as well as staffing costs for issuance of new, replacement, and temporary cards. These overheads all add up to a significant annual cost and for sites such as university campuses, there is a likely requirement to have one or more staff salaries to include in the total cost of ownership for managing physical cards.
“An alternative that is growing in popularity on some larger sites is digital credentials included on a smartphone,” Bell says. “A good mobile credential technology and infrastructure, such as Gallagher Mobile Connect has been designed to minimise the cost and effort in the management of access control credentials.
“The total cost of ownership includes the enrolment cost, which is similar to a card-based system, and the cost from the credential technology provider. Gallagher Mobile Connect uses a small annual per credential subscription that can be thought of as ‘Credentials as a Service’, similar to the now common Information Systems “software as a service” (SaaS) subscription.”
According to Bell, the cost benefits of digital credential systems like Gallagher Mobile Connect is that, once the information has been entered, the system will deliver the credential invitation to the person and manage the loading of the credential on the phone, removing the need for onsite staff costs. In addition, the overhead of reception having to issue temporary cards to staff members who have left their card at home is almost non-existent as it is unusual for people to leave their phone at home. Furthermore, Gallagher Mobile Connect also includes a secure photo ID card within the mobile phone app.
“Depending on the number of staff members within a site, the saving in cost could include one or more full time staff,” he explains. “These factors position mobile credentials as the lowest total cost of ownership for access control authentication use.”
While keypads are considered to offer only modest security levels, Bell says they may have a place in multi-factor authentication.
“Enterprise access control systems should have the capability for multi-factor authentication with after-hours access to a facility requiring at least 2 factors,” he says. “Where systems are using cards, 2-factor authentication will generally involve the entry of a PIN at the keypad. 2-factor authentication can be also accomplished with a reader biometric second factor, but these will generally be more expensive.
“Gallagher designed its mobile phone credential to also include the option for secure 2-factor authentication, where during the transaction the reader will indicate whether a 1 or 2-factor authentication is required. The mobile credential second factor uses the biometric sensor or a PIN on the phone, providing sites with after hours and secure area authentication without a keypad, resulting in added cost-savings.”

How has COVID-19 impacted on access control technologies, in Bell’s opinion?
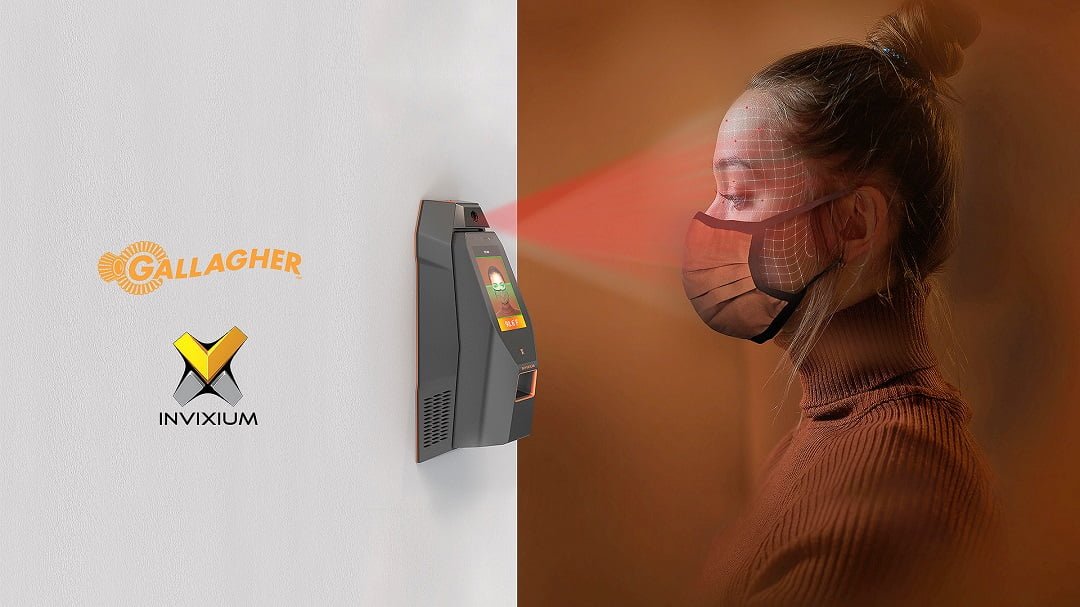
“The most obvious impact of COVID-19 is the desire for touchless readers, keypads, and biometric sensors,” he says. “Contactless fingerprint and facial recognition readers have grown in popularity for this very reason. Gallagher has a long-standing partnership with IDEMIA which manufactures a range of biometric readers. And in 2020, Gallagher integrated its Command Centre software with Invixium IXM TITAN, which offers temperature screening, mask detection, and face recognition while wearing a mask, to support sites operating within the ongoing COVID-19 pandemic”
In terms of outright security, it’s not always clear to users which authentication technology or combination of technologies offers highest security, but Bell argues the advantage lies with mobile devices for most applications.
“For general enterprise use, a mobile device with public key-based authenticator and embedded with a biometric is very secure,” says Bell. “I believe this is suitable for all but the highest level of government use. At the same time, Gallagher’s experience in protecting government sites requiring the highest level of security is that wireless personal devices will not be accepted. Instead, the use of card technology with keypad-PIN, fingerprint or IRIS is approved for use, but I expect face recognition will also become accepted in the future.
“Overall, there is strong indication that mobile devices and wearables will gain a market share in the future. As technology advances, more services are being provided through our personal devices and many of us are happy to access private information, such as internet banking, via secure authentication on our phone or wearable.”

Will Yeadon of Chase argues that access control is sufficiently diverse that different authentication technologies work better for different applications – there’s not a ‘best’ that suits all projects.
“Having said that, biometric authentication is a very secure form of access control,” Yeadon says. “The most secure biometric would probably be retina scan, however, this is not a commercially viable option. Something to consider is that high security generally does not offer inherent ease of use. Rather, it’s a question of what’s the best product for your particular application and the answers will vary considerably across the market. Personally, I think any multiple authentication is better than any single authentication, no matter how good it may be.”
According to Yeadon, COVID-19 has impacted on access control technologies in a number of ways.
“COVID slowed the industry, with many employees working from home, and it also brought a wave of new ideas and technologies, mainly touch-free entrance using facial technology, and increased no-touch request to exit,” he says. Despite these changes, Yeadon feels the keypad still has a place in access control installations.
“Being old school, yes I believe it still does, especially for a low-cost entrance under duress alert, and the ability to mandate keypad use via time zone, increasing the access level at different times of day or evening,” he says. “These qualities make keypads versatile, low cost, effective, but not for all projects.”
When it comes to whether or not card-only readers still have a place in the access control mix, or whether mobile device authentication is a better option for a carried authentication device, Yeadon argues cards continue to have a role.
“And I think using a phone for access is a good option and having an employee use their own phone for access has (economic) advantages, however, some employees may not want to use their phone for access without compensation,” he says. “Would it be unreasonable for staff to request a phone as part of their supplied uniform? Would the employer pay?”

Face recognition – is this the no-touch access authentication killer app, in Yeadon’s opinion?
“No, face recognition is cool and new, but so was iris, so was fingerprint and so was vein scanning and so on,” he explains. “Once enrolled, the biometric template will have to be updated every few years as the person ages out of the template threshold. I believe we are still in the honeymoon period regarding this re-enrolment with face recognition technology.”
In Yeadon’s opinion we will see a continuation of the technological proliferation when it comes to authentication in a fast-evolving world.
“I think so and I hope so,” he says. “When it comes to the latest developments, the use of mobile devices and geographical mapping for authentication is clever, especially with virtual meetings and the virtual world we are approaching. VR meetings and workplaces will be a new chapter to our lives with interesting security challenges when it comes to establishing who is in the meeting with you. Access control? Yes, Jim. But not as we know it.”
Meanwhile Nirovision’s Eliana Bettio sees significant impact on access control technologies from the COVID-19 pandemic.
“With better knowledge now of how germs and viruses spread from shared surfaces, many businesses are re-evaluating their access control system from a health and safety perspective,” she explains. “Old technologies, like fingerprint scanners and keypads, require regular cleaning, which is an increased time and cost burden to businesses. In addition, people have become more wary of touching anything, especially if communally used. For these reasons we’re seeing an increased demand for touchless solutions.
“At the same time, contact tracing requirements have forced many businesses to acknowledge they don’t know the number or location of people on their premises in real time. Keeping manual registries is resource intensive, error prone and insecure; there’s an incentive for businesses to explore access control solutions using biometric credentials, as an avenue to automate the collection of attendance and access logs. An added benefit of automating identification, health and compliance checks is the ability to be alerted upon inconsistencies or problems.
“Simplifying physical administration with digital processes is especially relevant in a post lockdown world, where face-to-face encounters to hand in swipe cards or enrol/unenrol user credentials won’t always be possible. Being able to perform key actions remotely, such as managing your database, replicate access levels across systems and audit activity is highly sought after.”

When it comes to choosing the most secure authentication combination, Bettio says that Nirovision believes any method of verification is greatly enhanced when facial recognition is added to the mix.
“This is because facial recognition relies on the right person with the right access being present, whereas cards, mobile devices and pin codes can be easily shared,” she explains. “In addition, with facial recognition, a workplace has video evidence of who accessed a door and if there were tailgaters, as opposed to standalone time logs that don’t tell the full story.”
And for Bettio, face recognition is the no-touch access authentication killer app.
“We might be biased, but we believe so,” she says. “While card readers and mobile phones are touchless alternatives, there is still the hassle of card maintenance and distribution. Meanwhile mobile phones are prone to battery issues, user error, and can be shared, stolen or hacked. Compare this to your face which goes everywhere you go, is unique to you and can’t be shared.”
#securityelectronicsandnetworks.com