Perimeter solutions push intrusion detection outside vulnerable facilities, increasing the length of time available for response to alarm events, as well as driving verification technologies, like PTZ presets.
Of the 4 defence lines defining site security, the first 2 include the protection of the perimeter fence and grounds of the site, and the protection of the walls, roofs and external fittings of the site’s buildings. In other words, perimeter security accounts for 50 per cent of a site’s 4-tiered security solution.
There are some sites on which the first line of defence are the walls of the building, but it still should be possible to move security outside a building to its approaches. A perimeter solution should cover gates, covered entries and driveways, as well as external sensors supporting walls, windows and doors. And physically harden up your doors and windows, incorporating vibration sensors to give early warning of physical attack on an entry point.
Physical barriers need not be only fences or walls. A creek, hedge, gully or natural wall can function as an excellent perimeter barrier when supported by electronic systems like AIRs beams, external microwave and video motion detection. A perimeter solution is not simply a detection technology on the end of an alarm zone – you also need to think about onsite reporting, as well as alarm monitoring and response.
According to Gallagher’s Adrian Chen, perimeter protection systems offer considerable operational value to security managers.
“Perimeter protection acts as the first line of defence for an overall security system,” Chen explains. “The key benefit of perimeter detection is the ability to detect an intruder before they enter your site. When a fence sensor is triggered, an alarm will activate for that zone, providing more time to respond and allowing guards to immediately focus their attention where it is needed most. A networked perimeter solution incorporates sensors that continuously monitor fence vibration or movement and can be used with or without an energised pulse to detect intrusion, without the intruder being aware.
“Perimeter solutions, especially those installed on the outer perimeter fence, provide the maximum time for monitoring stations and security patrols to respond to intrusion attempts, due to detection occurring as soon as an intruder attempts to enter the site’s boundary. The most important aspect of monitoring and security patrols is ensuring that they are responding to actual events and not false alarms.
“High levels of false alarms can lead to what we commonly refer to as false alarm fatigue, which is when security patrols are continually dealing with high volumes of false alarms, and as a result, they reach a point where their response is lessened through the assumption that it’s “just another false alarm, I’ll deal with it later”. This is where the selection of detection technology is key, and choosing a perimeter technology that works effectively, rather than making a decision based on price, is critical. Depending on the level of security required, combining multiple technologies such as Monitored Pulse Fence and VMS can improve co-ordination of the response.”
How difficult is it to integrate perimeter detection and protection systems with common security panels, in Chen’s opinion?
“Perimeter detection can easily be scaled from a basic alarm system to a fully integrated solution that provides additional information, such as maintenance alerts or voltage feedback on the fence line,” he says. “For instance, Gallagher Command Centre allows for seamless integration with other systems and third-party perimeter products.
“The capabilities of Command Centre extend from the fence line in, providing true site management from a centralised platform. A high-level interface between Gallagher’s Command Centre and perimeter security system delivers multi-site, multi-zone control and monitoring through a single graphical user interface.”
In Chen’s opinion, which sites are best suited to perimeter security systems?
“All sites that value their assets, should consider some form of perimeter/exterior protection,” he says. “From a dairy cooperative, to an airport, a local car yard, or a substation – sites of varying needs and sizes all benefit from perimeter security in some way, shape, or form.
“Critical infrastructure sites for example, are at greater risk of intrusion or sabotage and the shutdown of their facilities can affect hundreds of thousands of people. The protection of critical sites starts with a perimeter security system. In comparison, sites such as distribution centres or storage yards, are also at risk with potential knock-on effects to business continuity. Whether it be individuals trespassing a site to access parked vehicles and fuel tanks, or to intrude site buildings to steal goods – it all has an impact on the operational running of the business.
“The best defence is always executed from the fence line inwards, and perimeter detection is your first point of defence on the site. Site security is an integrated multi-layered solution consisting of perimeter security, CCTV, access control, and internal detection system. The most effective perimeter security solution comprises of multiple layers – from a physical fence, to video, disturbance/vibration, energised fence, taut wire, and a combination of multiple technology, each site is going to have its own individual requirements.”
Design philosophy that considers clear operational goals is vital when it comes to perimeter security.
“The operational goals of a business are critical when designing a perimeter system. If you do not understand the operational requirements of the site, you are relying on pure luck to solve your customer’s security challenges,” Chen says. “What perimeter security you implement for a warehouse facility may be completely different to a 24/7 airport facility or corrections facility. It’s imperative to understand what they are wanting to achieve, what process they have in place should an intrusion occur, the implications they face if assets were lost or damaged, their duty of care to the public, and how quickly the site can be secured if an intrusion takes place.
“By considering the operational goals of a business, you are better able to determine what technology, or combination of technologies, are required to secure the site, ensure reliable and timely detection, and be able to respond accordingly.”
Chen argues that in some cases powered fences are the best way to deter intrusion attempts on high risk, unmanned sites.
“Without a doubt, when it comes to perimeter security, it can generally be summed up with 3 Ds – deter, detect, and delay,” he says. “Without the 3 D’s, the perimeter system isn’t going to be as effective. As a result, there’s no more effective deterrent on a perimeter than an energised fence. Facing an obstacle that has 7000V–10,000V is a significant psychological deterrent, but unlike other deterrent technologies it is intentionally designed to be safe. It is the only system that can actively deter, detect, and delay an intrusion at the perimeter.”
According to Sektor’s Tom Kinkade, the primary advantage of perimeter surveillance is early detection and assessment of targets.
“Some technologies such as PSR can even provide 360-degree intelligence on airborne and ground-level targets as they approach a perimeter from 1000s of metres, allowing security response teams to ‘meet them at the fence’ or take necessary counter-measures,” he explains.
“In order to deliver meaningful perimeter security systems, professional security consultants determine the risk profile of their clients and then implement technology and a tailored concept of operations to meet the individual organisational needs.
“From our experience military, aviation, seaports, utilities, corrections, data centres and resources customers seem to be most concerned about implementing meaningful perimeter security.
“When it comes to perimeter, I don’t think any single technology is a gold standard, meaningful deployments take unique factors into account and often multiple techniques are used in concert to deliver the desired outcome.
“However, thermal cameras are the way to go in terms of accuracy, distance capability and consistency when compared to optical cameras. The best camouflage in the world is no match for a thermal camera. Moreover, thermal cameras are not affected by shadows, sun glare and scattered or moving light sources – all causes for degraded image quality and false alarms in the visible spectrum.”
According to Kincade, standard alarm panels are not the best solution for high security perimeter applications.
“Common security panels monitor binary sensor condition, i.e. open/closed,” he says. “This works well for traditional alarm sensors used on perimeters. On the other hand, large or high-risk locations may require enhanced situational awareness that can be garnered from perimeter surveillance systems. Dedicated systems can provide real time data on multiple targets including identity, classification, geolocation, speed, direction, friend/foe status and so on.”
According to Doug Kennedy of CRK, it’s not only high security sites that benefit from perimeter solutions – many SMEs have operations and facilities that can benefit from pushing the security system outside buildings for earliest possible detection.
“Perimeter systems are discreet, provide early attack warnings and offer alarm verification – best of all they don’t need to be complex or expensive,” he says. “One of the great advantages of the integration between Risco alarm panels and Dahua cameras is how easily they can be connected and integrated together to provide a perimeter security solution.
“Earlier detection of intruders gives time for security patrols to react and respond to intrusion attempts, especially on sites like factories and warehouses that have large areas to cover, where they also reduce the dependency on cameras and active patrols.”
Designing Perimeter Solutions
Man-made barriers must be employed if you need to deter and delay criminal entry. Fact is that regardless of whether your site employs PE beams, AIRs, microwave, optical VMD, external PIRs, capacitance sensors, fibre optic cable, thermal cameras, taut wire devices, monitored pulse fences, external dual technology sensors, fluid pressure systems, leaky coax; all should be installed in support of some form of physical perimeter barrier, whether it be a fence, wall, gate, grill or screen.
Exactly where the physical perimeter is located in relation to electronic sensing devices depends on your application. A defence installation is likely to have a physical barrier, a sensing field then a series of tight perimeter solutions around specific potential targets across a site. A prison on the other hand, will have its perimeter systems projected into the facility with electronic protection installed before the most significant perimeter wall or fence is reached by a potential escapee.
Many perimeter solutions will incorporate electronic sensing as part of the physical perimeter itself. Fibre optic solutions can either be buried or supported by a perimeter fence and are ideal if there’s a big perimeter that needs stable and reliable coverage at a competitive price. Taut wire systems, capacitive sensors, and fluid pressure sensors are all ideal for use in support of standard chain-link perimeter fences.
To provide reasonable security against opportunistic intruders a chain-link perimeter should incorporate a 3 or 4 stranded, barbed crown that slopes outward at 45 degrees to make entry into the site a more challenging proposition. The fence should use 9-gauge wire or heavier, and employ barbed lower strands. It should be at least 2m in height with a 2m support-post interval. Mesh size should not exceed 2 inches.
Any gap between the lowest wire and the ground should be at most 2 inches and you should seriously consider the ease with which loose soil can be scraped away to allow entry under the fence. If the funds aren’t available to anchor midsections between support posts to concrete sills, then they should be fixed to steel spikes driven deeply into the earth. When specifying barbed wire to support your electronic systems make sure you get 12 gauge, twisted double strand with 4 barbed points spaced at 4 inches and installed with strands less than 6-inches apart.
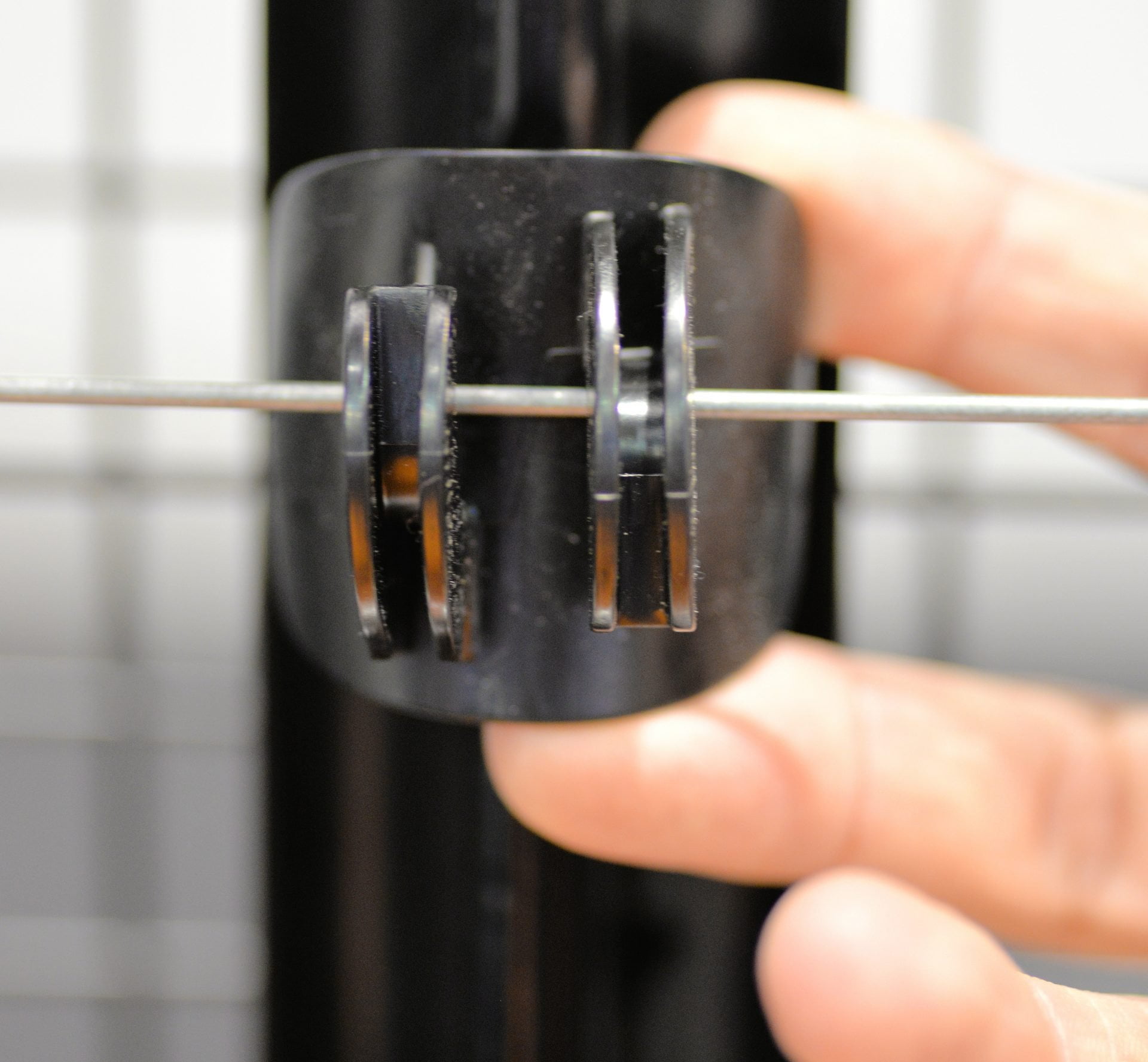
Electronic systems that can be installed in support of fence lines include pulse monitored, taut wire systems installed as part of the fence and positioned between a wire strand and a support post fixing point, or capacitive field systems, which employ an electrical field to create a stable EMI environment that intrusion will disturb. CPS systems are highly sensitive and can be used in higher security applications.
A particularly stable and relatively inexpensive solution is provided by the fibre optic cable sensors mentioned earlier. These cables can be installed directly on a fence (or buried). Pulsed light is fired down the fibre and if the properties of this light are disturbed by cutting or vibration, an alarm will be generated. The effectiveness of this sensing mechanism relates directly to the management software scanning the signal looking for aberrations in the ambient noise floor.
Every gate or access point in a site’s perimeter increases vulnerability to penetration and, if any electronic system is to be incorporated, increases the potential for false alarms. Effective electronic and manpower support of access points is the key to maintaining control. Within the limits of practicality, access points should be kept to a minimum. Doing so will mean fewer monitoring points, smaller gatehouse manpower requirements and fewer expensive long range access control readers.
Because breaks in the perimeter barrier are a weakness, special attention should be given to the construction, fixing points, and locking systems of gates. Electronic monitoring of access points is vital, and you should consider installing mechanisms like tyre shredders that render unauthorized vehicles leaving your site undriveable. Access point security levels should be greater than for your physical perimeter barrier, particularly in terms of physical strength.
There are a number of threats a perimeter system must be immune to, by virtue of technology, design and installation. The following factors will cause alarm in various perimeter systems – you need to manage these factors, or avoid them altogether:
* Passage of heavy transport
* Wind movement of tree branches
* Soil subsidence
* Microwave interference
* Inadvertent intrusion by kids, visitors or staff
* Fog, smoke, rain, fumes and dust
* Extremes of temperature
* Ice and snow
* Wind vibration
* Drying soils
* Ground movement generated by tree root movement
* Weight of rain water
* EMI and RFI
* Lightning
* Wind blown leaves
* Long grass, shrubs and bushes.
#sen.news











