What Are the Vulnerabilities Of OSDP In Access Control Applications?
What are the vulnerabilities of OSDP discovered recently, and what can we do as integrators to ensure our customers’ facilities remain secure?
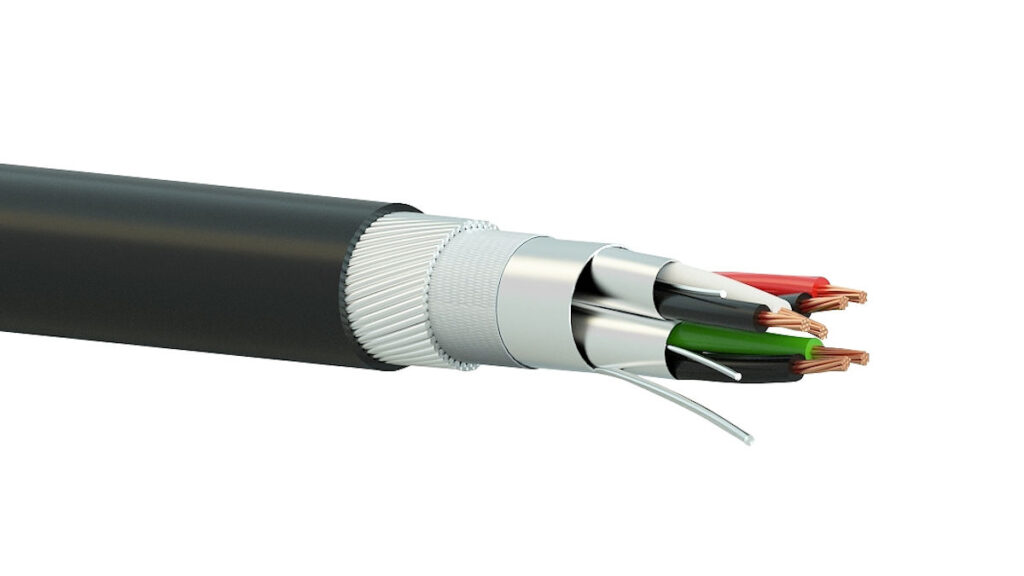
A: Open Supervised Device Protocol (OSDP) is an access control comms standard developed to improve interoperability among access control and security products and approved in 2020. It offers higher security thanks to the monitoring of cabling to protect against tampering and its support for AES128 encryption.
There were 5 key OSDP vulnerabilities and some lesser issues discovered recently by security consultant Bishop Fox and outlined by engineer Dan Petro. These issues mostly revolved around the nature of encryption between readers and controllers.
The first security flaw with OSDP is that security is optional for devices running OSDP protocols – you need to check and ensure the device/system you’re installing has encryption. While OSDP supports encryption, this does not mean the manufacturer of your solution has implemented it, or even that it was correctly implemented by techs during pre-commissioning and installation.
The second vulnerability outlined was a downgrade attack. What this means is that when a reader stands up in a system, the first thing it does is report its capabilities to the controller – for instance, whether it supports biometrics or whether it supports encryption.
This administrative message cannot be encrypted, so a device connected to cabling between the reader and controller can modify a reader’s capability message, which may include lying about the reader’s ability by saying it cannot support encryption.
This unencrypted reader then allows credential IDs to be skimmed by a device like an ESPKey installed between the reader and controller.
What Are the Vulnerabilities Of OSDP In Access Control
The third vulnerability is the install-mode attack. This happens when readers ask a controller for the base encryption key – a one-time unsecured setup step followed by secure communications. However, the researchers found many controllers are not configured with a step that forces integrators to exit install mode – the controllers remain in install mode. This means an attacker can instruct a device inserted into the system to simply request the encryption key from the controller.
The 4th issue found was weak encryption keys in OSDP implementations, including standard hardcoded keys that were never updated by commissioning techs whose sample code may be found online.
According to researchers, there are around 768 such hardcoded keys that could have patterns like:
- All single-byte values: [0x04, 0x04, 0x04, 0x04, etc]
- All monotonically increasing byte values: [0x01, 0x02, 0x03, 0x04, etc]
- All monotonically decreasing byte values: [0x0A, 0x09, 0x08, 0x07, etc].
The 5th vulnerability is keyset capture, which emerges from the fact OSDP has no secure in-band mechanism for key exchange and there are currently no out-of-band mechanisms, either. As a result, the way a reader gets the base key it uses to work out session keys is for the controller to transmit that over cables that may be vulnerable to attack.
This vulnerability allows attackers to break, factory reset, replace, or otherwise decommission an RFID reader and when techs replace it, a listening device installed between the reader and controller can record the keyset message transmitted between the new reader and the controller.
Defending OSDP Applications
From an integrator’s point of view, you need to be sure you’re using a system in which OSDP encryption is not only supported but has been correctly implemented and commissioned on your devices.
Checking configuration on OSDP controllers may not be a simple matter and will vary across devices, as each manufacturer of OSDP-compliant systems has its own interpretation of the standard.
Integrators need to check the configuration of OSDP controllers and establish not only what the security configuration is, but what it’s called and what its capabilities are – manufacturers will be able to help if you get stuck.
You’re also looking to ensure the controller refuses any connection from an unencrypted reader. And you want to ensure install mode is only enabled when installing a new reader and there’s a process that forces the controller to be taken out of install mode.
What Are the Vulnerabilities Of OSDP In Access Control
Of all the vulnerabilities, researchers found keyset capture was the trickiest attack to protect against and one that can’t be resolved by config. They advised that security monitoring teams and security managers should never ignore tamper alarms from readers but should assume any tamper is a potential attack.
Any reader suddenly going offline should be treated with considerable care – if possible check vulnerable sections of cable where a listening device might be connected. When replacing readers they recommended taking the reader to the controller and hooking it up using a short commissioning wire.
What are the vulnerabilities of OSDP Conclusion?
It’s worth noting that OSDP has greater security potential than Weigand and that OSDP applications in access control systems will vary. You’d expect proprietary applications of readers and controllers to be far more uniform than mix-and-match solutions.
For this reason, it’s undoubtedly justified for serious manufacturers to consider developing their own reader-controller secure comms technologies, and it’s certain that these solutions would be easier for technicians to apply reliably.
OSDP is an evolving security standard whose application depends on development from manufacturers and thoughtful commissioning by integrators working towards fixed security goals provided by security managers. OSDP is not an out-of-the-box secure path between readers and controllers.
Integrators and security managers may think the flaws outlined here are mostly secure side attacks requiring technical nous, and there’s a certain truth to that. However, for secure sites facing credible risks, care must be taken to mitigate reader vulnerabilities projected right to the edges of a secure perimeter.
You can learn more about the Bishop Fox report on OSDP or read more SEN news here.
“What Are the Vulnerabilities Of OSDP In Access Control Applications?”