What’s The Most Important Security Technology?
What’s The Most Important Security Technology? What’s the most important electronic security technology when it comes to meeting the needs of security management?
The most important security technology for security management – and all end users – is the one that best meets achievable operational outcomes. There’s much more to think about here than just installing a system – you need to discover what security management is trying to do and decide which system is best going to help them do it.
Making this complicated is that security managers may be unsure of technological possibilities, or they may overreach. In other cases, a facilities manager outside the security function may have oversight of a security integration and may on the integrator to provide a solution fit for purpose. And there are going to be times in SME applications where a ‘security system’ is required but no one has any clear idea what it needs to do, or why.
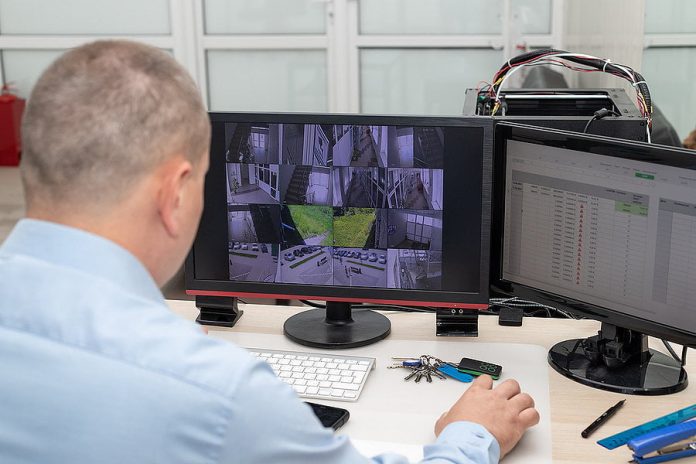
When you think about site security, it’s very easy to imagine applying access control to doors, alarms to interiors, and video surveillance to building approaches or areas requiring safety and security. But simply installing systems does not magically create a live security function with a capacity for risk assessment, creation of procedures, response, investigation, oversight, reporting, training, real time communication and the rest.
Good security consultants and security integrators know that capable electronic security systems are part of something larger – a strategy created to facilitate security and safety. Each security controller, device, server, piece of software, cloud application, must at once support and express this core security strategy.
The most important elements of security technology from the point of view of security management don’t involve technology at all – they revolve around considerations of risk and responsibility, the creation of thoughtful procedures, and careful consideration of the ways in which security technology can be used to deliver realistic operational outcomes in the most secure, reliable, economical and manageable ways.
#SEN #SENnews #security #electronics