Axis Patches Vulnerability In A1001 Door Controller.
Axis patches vulnerability – Axis Communications has patched a vulnerability in its A1001 network door controller.
The vulnerability was found by cybersecurity experts from OTORIO, who said it “involves the way A1001 communicates, potentially exposing sensitive networks to unforeseen risks”.
“Such a flaw could pose a significant threat to facilities’ security and their internal IP networks,” OTORIO told NVD. “This discovery sheds light on potential risks to highly fortified OT networks, unintentionally blurring the line between physical and digital security.”
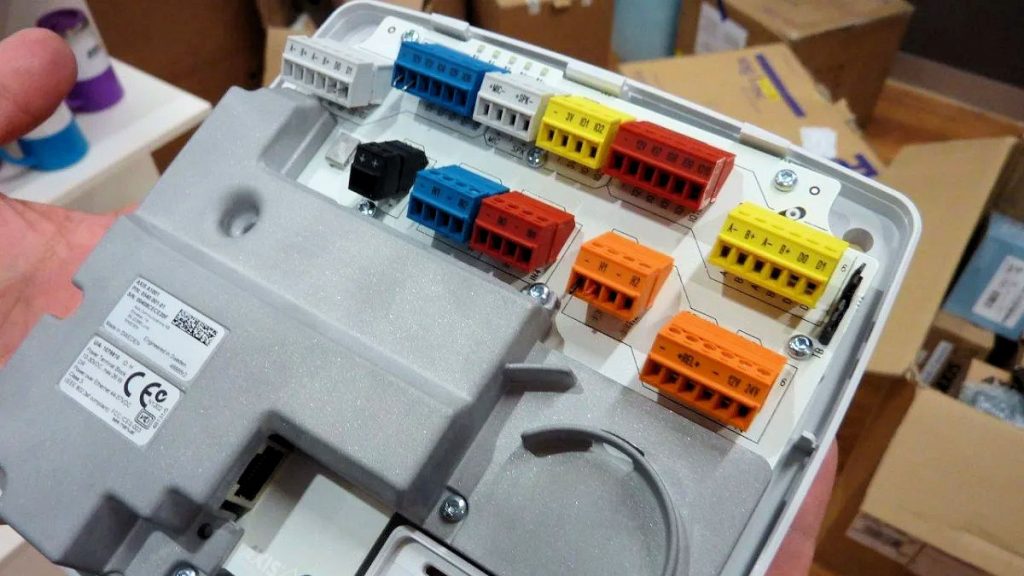
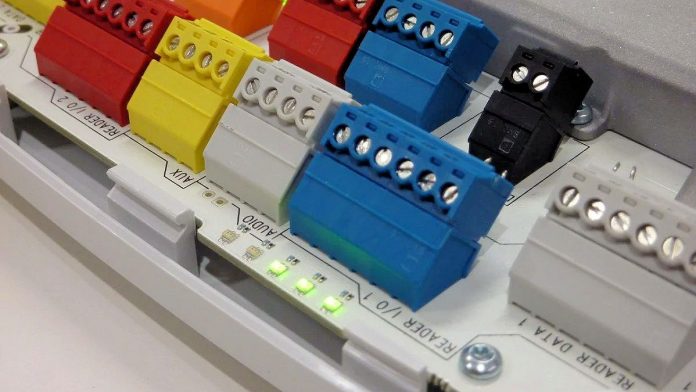
According to OTORIO, the vulnerability requires physical access to the RS-485 twisted pair cable situated at the rear of access control readers, which are often located at entry points outside a secure facility.
“What sets this vulnerability apart is its potential for remote code execution (RCE) on the internal access controller from outside of the facility,” OTORIO said in its report to NVD.
“By exploiting the serial channel used for reader-controller communication, an attacker could gain unauthorized access to open doors or tamper with logs on the access controller – this flaw could serve as a gateway to the internal IP network, irrespective of its segmentation or air-gapped status from the internet,” OTORIO said.
Axis Patches Vulnerability In A1001 Door Controller
An Axis Communications spokesperson said the company is confident it has now addressed the problem.
“Ariel Harush and Roy Hodir from OTORIO found a flaw in the AXIS A1001 when communicating over OSDP,” the spokesperson said. “A heap-based buffer overflow was found in the pacsiod process which is handling the OSDP communication allowing to write outside of the allocated buffer.
“By appending invalid data to an OSDP message it was possible to write data beyond the heap allocated buffer. The data written outside the buffer could be used to execute arbitrary code.
“The vulnerability was assigned a 7.1 (High) severity via the CVSSv3.1 scoring system. Accordingly, Axis has addressed the vulnerability by releasing a patched version for affected devices that increases robustness of the OSDP message parser and patches the highlighted flaw.
You can find out more about the A1001 door controller vulnerability, as well as Axis open vulnerability management policy here or read more SEN news here.
“Axis Patches Vulnerability In A1001 Door Controller.”