Like all good fairy tales, we begin with “Once upon a time…” Once upon a time, security systems were analogue and not connected to anything, or at most, a phone line, cameras connected to a time lapse VCR, and we saved footage on shelves full of video tape.
IT’S now 2016 and most security systems are network or internet-connected, yet it’s still far too common for people in the security industry to believe we’re living in a fairy tale world typified by a comment I recently read suggesting that physical security can survive without cyber security. However, in the world of modern security systems everything is a computer.
Acknowledging that there’s an element of hyperbole in that statement, let’s consider some of the key aspects that would have us consider a device to be a computer:
• It has an operating system
• It receives and processes information
• It is connected to a network.
Once everything is a computer, it’s all susceptible to a wide array of cyber-attacks from both internal and external threat actors. In modern CCTV systems we find servers and workstations, typically running a Windows operating system. All IP cameras have an embedded operating system, most often Linux, and typically stream images via one of a number of standard protocols such as RTSP. This is all just standard computer network traffic, not much different from watching YouTube or Netflix. Systems will often include network switches, storage devices, and internet routers.
While alarm detection devices have changed little, most alarm and access control panels are now network connected and in large access control environments, most often controlled from a Windows server and workstations. Alarm transmission equipment frequently uses mobile data or an internet connection to relay signals back to monitoring stations; and card readers often use computer networks for communication with the control system.
We have mobile apps that let us stream footage, arm and disarm alarm systems, or even unlock doors. We use Wi-Fi, wearables, and tablets all of which may or may not be particularly well secured. Every IP camera, IP controller, server, workstation, network switch, POE card reader and internet connection is a point from which a criminal could try to attack these systems.
One of the reasons that the physical security industry has remained relatively immune to cyber-attack thus far is less about difficulty than it is about motivation. In February 2016, the Hollywood Presbyterian Medical Center in LA suffered an attack on its computer systems that prevented them accessing patient records, prevented them using their CAT Scanners and had staff relying on pen, paper and fax machines to run the hospital.
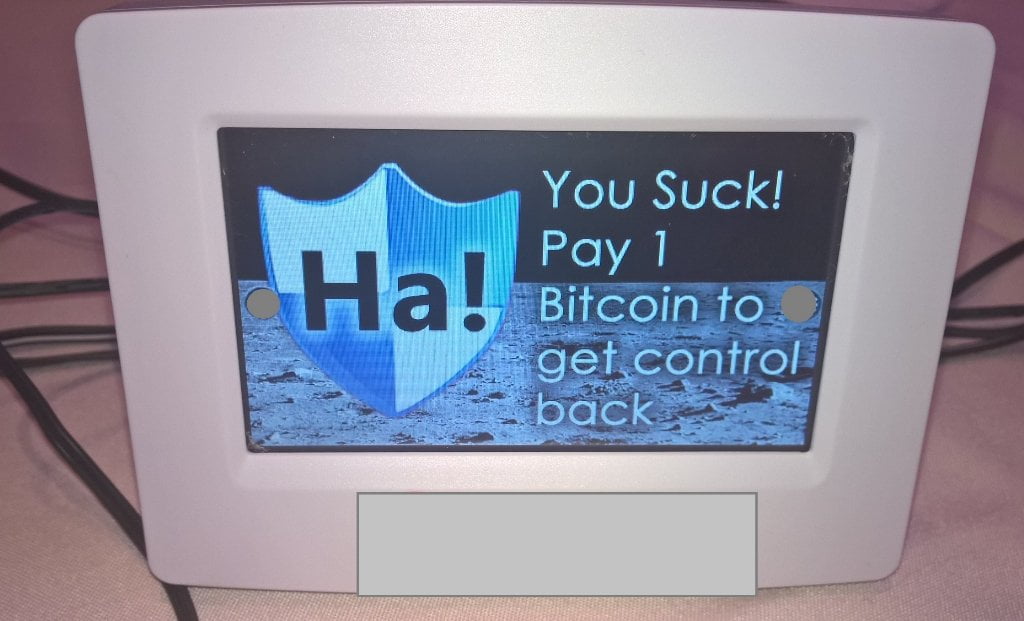
A recent proof of concept attack demonstrated the installation of ransomware an air conditioning system thermostat with the proclamation “You Suck! Pay 1 Bitcoin to get control back”. With criminals looking for opportunities for profit, a ransomware attack on a CCTV or security system is highly conceivable. What would an organisation be willing to pay to get its CCTV footage back or regain control of their access control system? And why would an attacker need to “Mission Impossible” their way into a site if they can just log in with admin / admin, disarm the alarm system, stop the cameras recording, and unlock the doors.
Internet facing devices can be used as a source of free computing resources. In the recent Miria Bot Net attacks, we saw the devastating impact that poorly designed or implemented security equipment can have with over 500,000 internet-connected cameras, DVR’s and other IoT devices launching one of the largest ever Denial of Service attacks.
There is a great deal that can be done to protect security systems, much of it not all that difficult or time consuming. The below are some quick easy wins to improve the cyber security of a physical security system. Servers and workstations should be kept current with operating system updates and have anti-malware software installed. Legacy operating systems such as Windows XP and Windows Server 2003 should be replaced or upgraded. There should be complex passwords on systems and other basic information security measures in place.
If there is any sort of network storage used to keep incident footage, reports, backups or other valuable information, ensure there is a strong password in place and that anonymous connections are not permitted. On systems of any appreciable size, system configurations should be backed up and stored on a separate system, removable media, or secure cloud storage, as rebuilding a system can take many days of work. Cameras should have default passwords changed – not just the admin or root password, but any other default passwords as well. I was very pleased when I set up a camera the other day and it not only forced the password to be set on first login, but enforced minimum complexity requirements for the password.
An attacker with physical access to any part of an open security network (which is the way they are most often configured) can traverse the network to all the other devices. Accessible cameras, card readers, and networking equipment should be secured and made difficult to tamper with. Siren housings, despite the fact that hardly anyone takes notice of them anymore, still come with tamper switches yet in CCTV systems, this is almost never considered.
When security systems are connected as part of a larger network, consideration should be given to how the various systems need to be protected from each other. Could a compromise on the CCTV network allow an attacker to access a corporate network? Or can a curious IT help desk technician view cameras in areas to which they shouldn’t have access? The use of VLANs and other network segregation techniques is essential when security equipment is part of a broader IT infrastructure. Finally, we need to consider the physical security of these systems. Network switches in public spaces, unlocked workstations at vacant reception desks, and servers in unsecured rooms are all easy targets for an attack that is likely to go undetected.
No one can argue that there are a lot of challenges in securing these systems as they typically have long service lives and are not all that easy to update. If a vulnerability is found in the firmware of a given brand of camera, updating the firmware in all the cameras can be a costly and time consuming exercise for a site. The simple task of changing passwords on CCTV cameras can be a time-consuming process requiring updating passwords on individual devices, updating each camera in the video management systems, and sometimes, standing atop a ladder trying to power cycle a camera, press and hold a reset button, and not drop anything while doing a factory reset.
None of these challenges are unique to the security industry, with SCADA systems, production plants, factories, and critical infrastructure all dealing with similar challenges. These industries have seen power grids compromised by nation states, nuclear power plants with malware in their systems, credentials for hydroelectric systems being sold on the dark web, and almost a million litres of raw sewage being released into local parks and rivers.
While manufacturers are starting to build security features into their offerings, these are frequently proprietary and fall back to non-secure protocols when used with other systems. The IT industry has had many years of experience in developing and implementing robust security and cryptographic solutions that the physical security industry should be leveraging.

In order to transform cyber security standards in the physical security industry, manufacturers and integrators need to recognise that robust non-proprietary cyber security controls are becoming a differentiator when choosing a security solution. In addition, they need to make securing a system easy and in place by default rather than requiring a complex and time consuming process.
As security technology becomes more and more IT connected and reliant, the difference between physical and cyber security will continue to diminish. With security being the business of protecting assets from harm, the staff from the traditional security industry often have a better understanding of risk, threat actors, and identifying valuable assets than IT specialists being given security responsibilities. Rather than seeing cyber security as a problem or challenge, the security industry should be embracing cyber security as the next great opportunity. ♦
*Simon Pollak is a security professional with more than 25 years’ experience in physical and cyber security, smart buildings and automation systems. A licensed security consultant, he holds a Masters of Cyber Security and a Masters of Business Administration (Technology). Simon writes a monthly article in SEN discussing all things cyber security.